On October 14, 2025, multiple media outlets (CNET, WIRED, etc.) reported that research teams from the University of California, San Diego, and the University of Maryland, College Park, intercepted unencrypted calls and text messages of T-Mobile users, US military communications, and even control commands of the Mexican power grid from space using a set of inexpensive amateur equipment costing $800.
Based on this, researchers published a groundbreaking research paper - "Don't Look Up: There Are Sensitive Internal Links in the Clear on GEO Satellites" - at the ACM CCS 2025 top-level security conference, and used the movie Don't Look Up to warn that there are security blind spots in the current satellite communication ecosystem.

▍Research Background: How Low-Cost Equipment Can Unlock Space Secrets
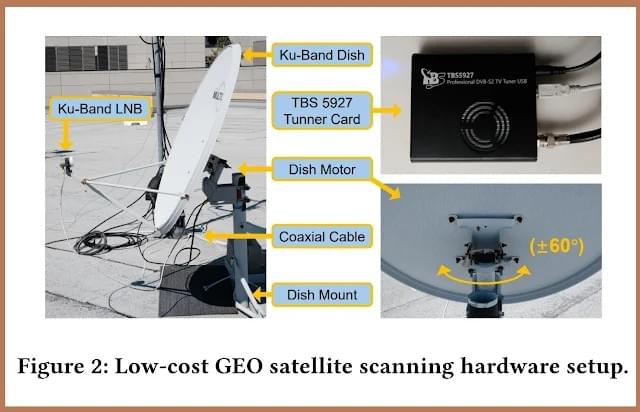
The research team set up a receiving system with a total cost of less than $800 on the rooftop of a university, including an $180 Ku-band satellite antenna, a $15 low-noise downconverter, a $195 motorized rotating mount, and a $230 tuning card.
The paper states: "Traditional views hold that satellite interception requires national-level resources, but we prove that low-resource attackers can use commercially available off-the-shelf equipment to passively scan a large number of GEO transmissions."
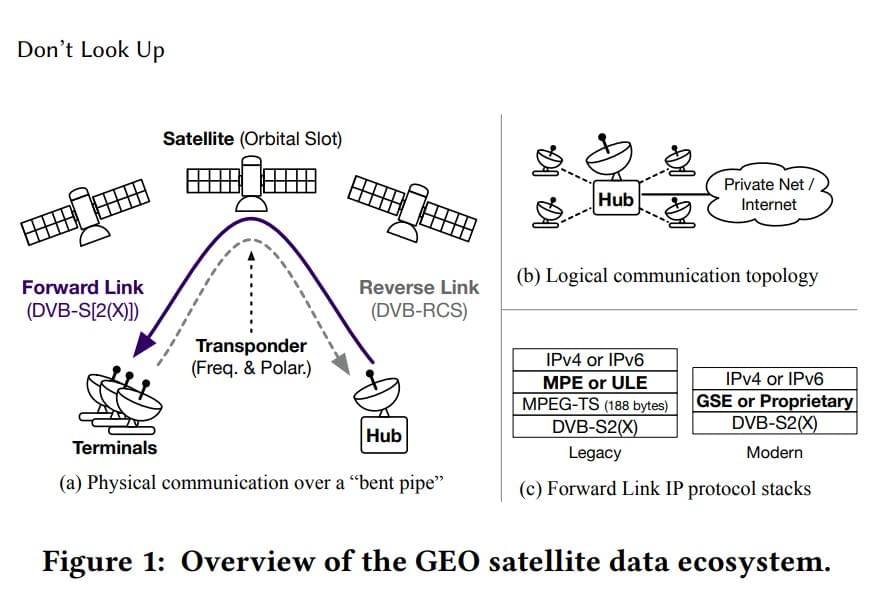
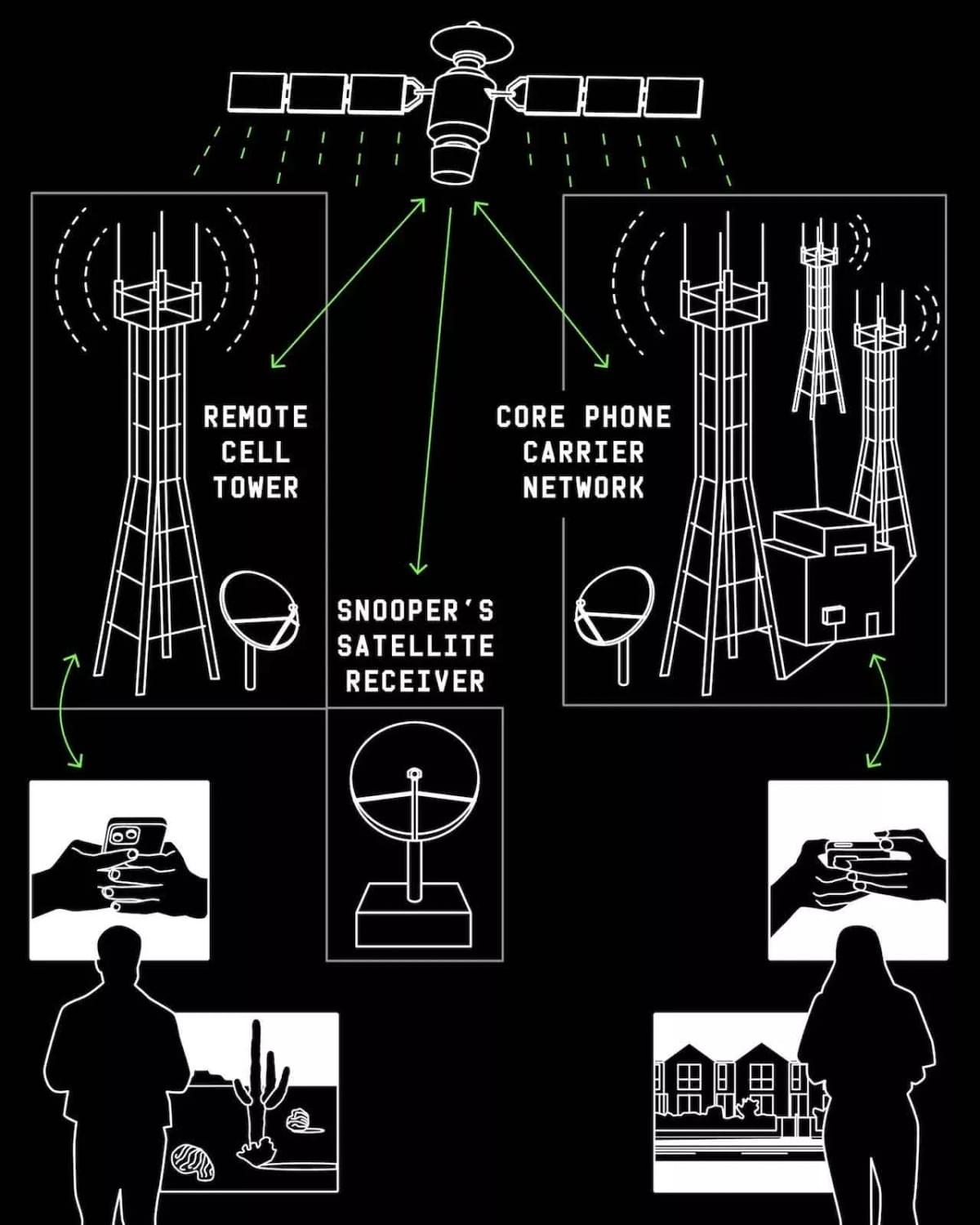
The core of the vulnerability lies in the architectural design of the satellite postback link - when base stations in remote areas postback traffic via satellites, it is unencrypted: the link from mobile phones to base stations is encrypted, but the satellite segment from base stations to the core network is "naked". And the coverage diameter of satellite transponders can reach tens of thousands of kilometers.
source: www.wired.com
Researchers at a single observation point in La Jolla, California, can receive signals that were supposed to be sent only to base stations in Mexico or remote areas of the western US. The paper states: "These signals are being broadcast to over 40% of the Earth's surface." This means that it's not just the researchers' location that can intercept them; theoretically, any point within the entire satellite coverage area can conduct the same eavesdropping.
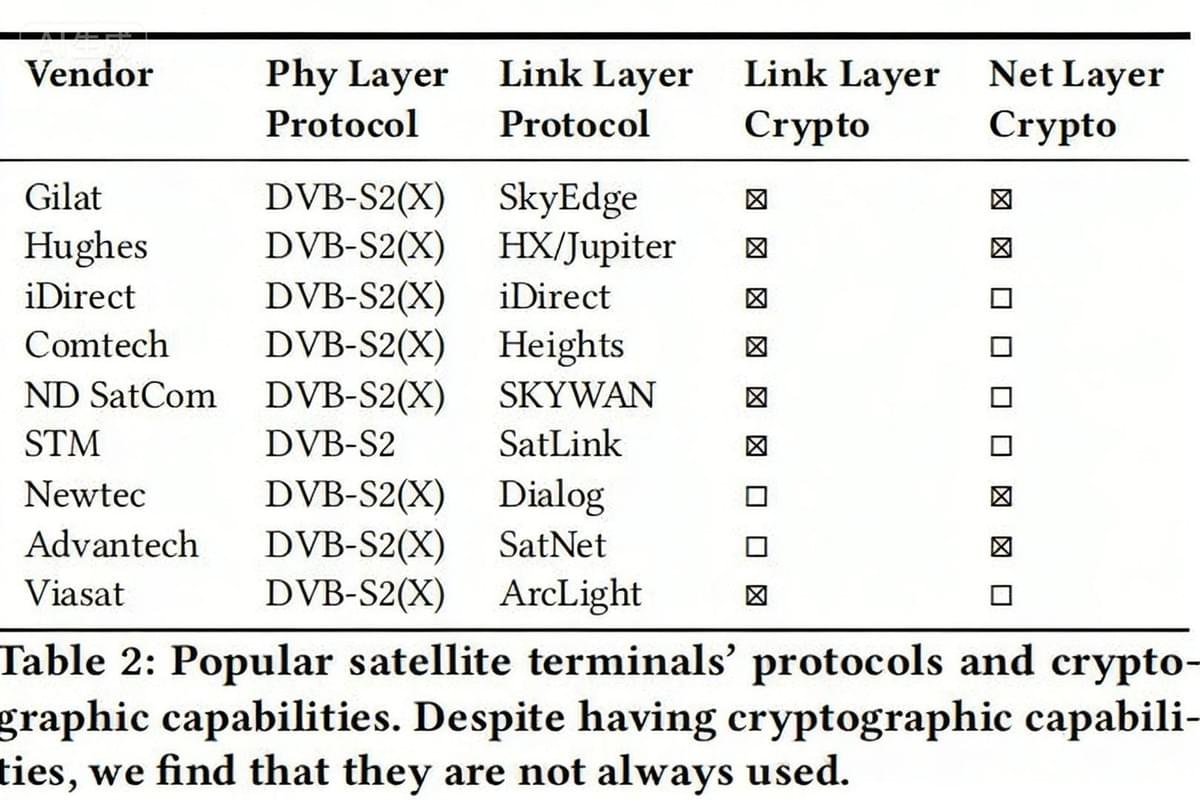
Meanwhile, since different manufacturers use their own proprietary and non-standard protocols, such as the "non-standard length field" (2 bytes shorter than the standard) and the "6/2 fragmentation identifier" (the first 6 bits identify the PDU, and the last 2 bits identify the fragmentation offset) in GSE encapsulation, the research team developed a universal parser capable of blindly parsing seven different protocol stacks, five of which were publicly parsed for the first time. Previous research was limited by signal quality and protocol diversity, while the new method cracked the manufacturers' proprietary protocols through reverse engineering, which is precisely the key to the increase in the success rate of IP packet parsing from 15% to 69%.
▍Data Leakage Scale: Half of Satellite Links Transmit Data "Naked"
The results of the monitoring scan are shocking: approximately 50% of GEO satellite links transmit IP traffic without encryption, while satellite TV content is generally encrypted due to anti-piracy requirements. The paper's statistics show that among 346 non-TV transponders, only 6% use IPsec encryption, 20% of GSE protocols have encryption enabled, and the rest are broadcast in plain text.
Researchers explain this phenomenon with "structural incentive deficiency": satellite TV has a clear economic incentive to encrypt, while enterprise networks treat satellites as ordinary internal network links, ignoring the broadcast characteristics of space transmission.
Moreover, satellite postback networks are usually operated through multiple service providers, and the suppliers are numerous and complex. For example:
- T-Mobile leases transponder bandwidth from a satellite provider.
- This supplier may use Hughes or iDirect end point devices.
- The encryption feature in the device may be an "optional module" that requires additional authorization.
Finally, the dynamic changes in transponder deployment have exacerbated risks. Comparing the scans from August 2024 and February 2025, the transponder replacement rate of some satellites exceeded 30%. For example, 8 transponders disappeared at 129.0°W longitude, and 10 new ones were added at 105.0°W. This fluctuation indicates that operators frequently adjust service leases, but security configurations have not kept pace. As researchers have stated, "Satellite security research still requires a continuous monitoring paradigm; static snapshots are not sufficient."
▍T-Mobile Case: How Call and Text Messages Are "One-Way Wiretapped"
The most eye-catching incident is the T-Mobile data breach, where researchers intercepted the call metadata and SMS content of over 2,700 T-Mobile satellite users.
The core of the vulnerability lies in the architectural design of the satellite postback link, that is: when base stations in remote areas postback traffic via satellite, it is not encrypted; the link from mobile phones to base stations is encrypted, but the satellite segment from base stations to the core network is "unprotected". Since the coverage diameter of satellite signals can reach tens of thousands of kilometers, an antenna in California can receive traffic that should have been sent to a base station on the Mexican border.
Specifically, T-Mobile's satellite beams are transmitting their postback traffic in an unencrypted manner. Its protocol stack is: DVB-S2 (physical layer) → proprietary encapsulation layer → IP → GTP tunneling layer. It is precisely this proprietary encapsulation layer and GTP tunnel that are unencrypted, leading to data leakage.
The leaked data includes clear SIP signaling and RTP voice streams. For example, the protocol stack of a text message shows that the SIP message method contains the plaintext content of the GSM-encoded text message. However, the interceptor can only hear "one-way conversation" - that is, the downlink traffic sent from the core network to the base station, while the uplink traffic needs to be captured by another antenna close to the target base station.
T-Mobile responded that the issue was limited to approximately 50 base stations of a certain supplier and quickly enabled network-wide SIP encryption. However, the research team pointed out that "such vulnerabilities may exist in multiple operators but have not been detected."
Since satellite communication uses a "star topology," all communication from end points (cellular base stations) must be forwarded through the central hub (Hub). The researchers intercepted the "forward link" from the T-Mobile core network to remote base stations. This means they can only capture downlink traffic, i.e., data sent from the network to mobile phones (such as call requests, downlink SMS content, and internet data packets sent to mobile phones), but cannot directly capture uplink traffic sent from mobile phones to base stations.
Protocol Analysis:
- User plane traffic (S1-U): It exposes raw Internet data, but most user App traffic (such as browsing a web) is already encrypted by itself due to the use of HTTPS/QUIC/TLS, thus avoiding content leakage. However, metadata (DNS queries, destination IP addresses) is completely exposed.
- Control plane signaling (S1-C): Carried over SCTP (port 36422), researchers have parsed out S1AP protocol messages. These messages perform functions such as establishing the mobile context, reporting protocol errors, paging, and carrying encrypted NAS signaling.
IMS Service (VoLTE Voice and SMS): This is the most serious leak. Researchers found that SIP signaling is transmitted entirely in plaintext, exposing the calling and called numbers, call session metadata (Call-ID, CSeq number), and SDP details (such as negotiated RTP ports, codecs). Although IMS traffic has an IPsec layer, its encryption algorithm is configured as "null cipher", rendering it ineffective.
RTP voice stream: unencrypted , allowing the actual call content to be directly decoded and restored.
- SMS Content : The 3GPP 7-bit encoded GSM SMS format is transmitted in plaintext within SIP messages and can be decoded for reading.
How to determine if it is T-Mobile:
During 9 hours of monitoring, researchers observed the phone numbers of 2711 users from metadata. They could hear clear one-way call content and read complete text messages. Through S1AP signaling, they could also obtain unique identifiers such as the International Mobile Subscriber Identity (IMSI) of the mobile phone. Finally, they identified it as T-Mobile through the MCC (Mobile Country Code) and MNC (Mobile Network Code) in the message.
▍Breadth and Severity of Leaked Data
Researchers intercepted various types of data, including:
- Military Deployment: Unencrypted data froS military ships and Mexican military and police, including military asset tracking, personnel deployment, and even intelligence on anti-drug operations. For example, transmissions from the Mexican military include the locations, mission logs, and real-time telemetry data of Mi-17 and UH-60 Black Hawk helicopters. This information was leaked through commercial satellite postback links.
- Government Infrastructure: Work orders for the power grid of Mexico's state-owned electricity company CFE, customers' personal information, equipment failure reports, etc., are all transmitted in plaintext. The control system communications of Mexican oil platforms and power facilities are also fully exposed. After the research team reported this to CERT-MX, some institutions still failed to fix the issues.
- Business Secrets:Walmart Mexico's inventory management system transmits unencrypted telnet login credentials, FTP inventory records, and internal emails via satellite, leaving SKU codes and sales data fully exposed. In the ATM communication of Santander Mexico Bank, LDAP authentication data and internal domain names flow in plain text.
- Civil Aviation Sector: Panasonic Avionics and Intelsat's in-flight Wi-Fi data includes user browsing metadata and unencrypted audio from news programs. Researchers even recovered the RSA private key from fragmented data.
▍Summary
Operators such as T-Mobile generally adopt a hybrid network architecture that includes the DVB-S2 physical layer and cellular satellite postback (such as base station - core network satellite links), and the devices supporting this architecture, such as end points and hubs, come from at least 10 different suppliers, with each vendor using its own proprietary protocol stack, resulting in a highly fragmented vendor ecosystem .
At the satellite link level, the issue of protocol fragmentation is prominent - not only do old and new physical layer protocols such as DVB-S (legacy) and DVB-S2 (X) (modern) coexist, but there are also non-standard implementations of the GSE protocol such as "6/2 fragment identifier" and "length field offset by 2 ByteDance"; combined with the lengthy supply chain of "satellite owner - transponder lessor - end point supplier - operator" and the technical contradiction of "mature satellite TV encryption but lack of IP link encryption", risks in a single link (such as unencrypted protocol at a certain layer or configuration errors) are continuously amplified, ultimately leading to a global security incident.
As the metaphor in the paper “Don't Look Up” warns —— the industry has long relied on the false security of “no interception of satellite links” , but only a set of low-cost civilian equipment (about $800) and one active scan are needed to shatter this illusion, exposing the systemic security vulnerabilities of the entire satellite communication industry .
Reference Materials
- <> https://satcom.sysnet.ucsd.edu/docs/dontlookup_ccs25_fullpaper.pdf>
- https://www.wired.com/story/satellites-are-leaking-the-worlds-secrets-calls-texts-military-and-corporate-data/
- https://www.cnet.com/tech/services-and-software/satellites-have-exposed-sensitive-data-from-t-mobile-and-others-research-reveals/
- https://5gstore.com/blog/2025/10/14/t-mobile-data-exposed-via-satellite/
